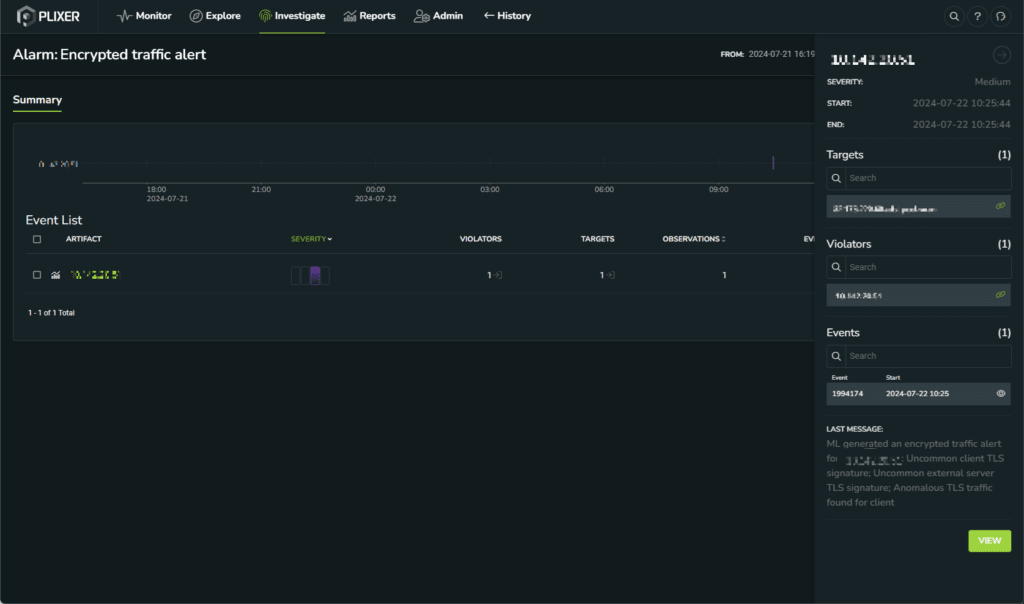
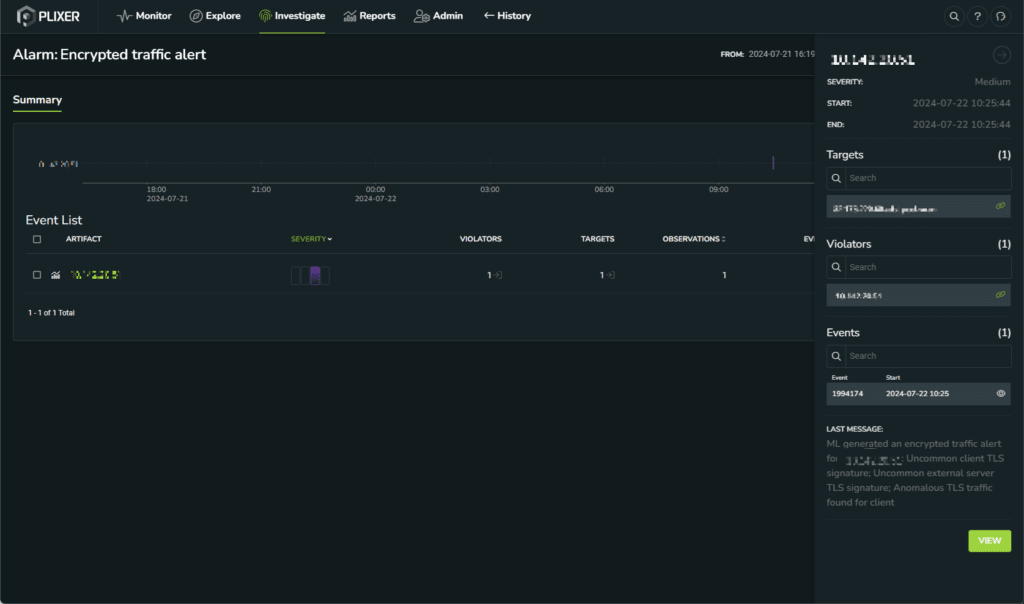
Author: Erik Peterson, Sr. Director of Engineering at Plixer Experience Network Detection and Response with Plixer’s Latest Release: Plixer 19.4 ML Engine August 2024 marks an exciting milestone for Plixer customers seeking to enhance security with the .



Elevate your network performance and cybersecurity know-how. Sign up for our blog to unlock exclusive insights, expert analysis, and actionable NMPD and NDR tips.

Author: Stephanie Kille, Customer Success Manager, Plixer Recent years have seen a disturbing trend of healthcare data breaches, with cybercriminals targeting organizations across the.

Here at Plixer, we are redefining what it means to know your network. Today’s networks are becoming infinitely more extensive and dynamic as data.

The digital landscape can sometimes seem a bit like a dense forest after dark, with new and unseen threats potentially lurking everywhere. That’s why.
Every year, there is a greater number of breach disclosures. Some do so for the first time; for other organizations, it’s the latest in.

In an ocean of data and interconnected devices ranging from physical and virtual networks to the cloud, ensuring complete visibility and monitoring of your.

In today’s complex cybersecurity landscape, the battle between hackers and defenders is a continuous chess match. Recent revelations about the “Decoy Dog” exploit have.
Dive into the recent HCA data breach and learn how a zero-day attack can quickly cause damage to your business.

By now you have probably heard of a vulnerability in MOVEit or its use by the hacking group ClOp. This cyber attack is all.

Endpoint security is crucial for protecting your organization from cyber threats. With the increasing vulnerabilities posed by human actions, it’s essential to have key.